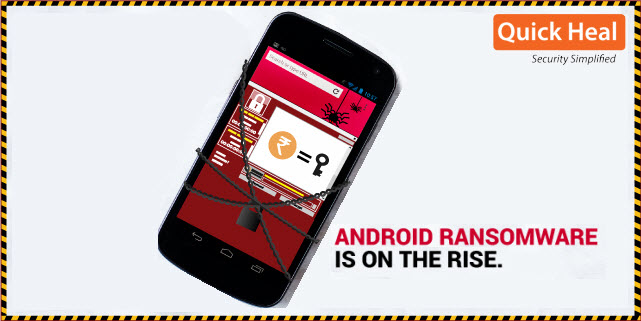
Beware of these fake apps on Google Play Store that use ‘Jio/Jeo’ in their names
Jio took the Indian telecom market by storm when it made its entry with free unlimited calls and data offers. People went into a kind of frenzy for acquiring this service. And with its ‘truly unbelievable’ offers, Jio also launched an array of apps on Google Play Store such as Jio4GVoice, JioChat, JioMusic, etc. And […]